Here we describe the process we followed to obtained a secure badge of one
of the participants. A high resolution of the pictures is available here

| Every participant to WSIS follow the signs to the registration desk. The participants were requested to
carry the LETTER OF INVITATION that includes a REGISTRATION NUMBER and an IDENTITY CARD. |

| The participants stand in a queue and provide a REGISTRATION NUMBER. The REGISTRATION NUMBER is checked
against a database. The participants show an ID Card and a picture is taken of them via a Webcam.
In our case we "only" provided the name of an existing participant that we obtained from the WSIS website and show a
plastic card (as a secure ID Card) that contain the name of the participant and our picture. |

| While we asked about the WSIS PRIVACY POLICY concerning the collection of personal data and what the badge contained, we did even have time to
picture all the cameras. No extra information was obtained upon our request |
| NOONE INFORMED us in advance about the procedure, that our picture was going to be stored in a DATABASE and the period of data
retention. NOONE INFORMED us that the badge contained a SmartCard and a Radio Identification (RFID) built-in that could be triggered remotely without the cardholder noticing. The badge is printed out in less than one minute. The whole procedure takes around 3 minutes. |

| By this time we had a badge of one of the participants containing our own picture. We spent the following days making
an analysis of what the badge contained. The control system is composed of a Radio Reader and a terminal. The Radio Reader exchanges secure messages with the badge of the participants. |

| When a participant approaches a radio reader a set of transations takes place in the centralized database. In the entrance, the associated picture to the name of the participant is retreived. Other data of the participants is also retreived as the name, affiliation and the times has entered the Congress. The system allows by datamining to obtain the human relationships of the participants. |

| Detail of one the proximity radio sensors. Sensor can be placed in the entrance of sessions rooms or a vending machine. |

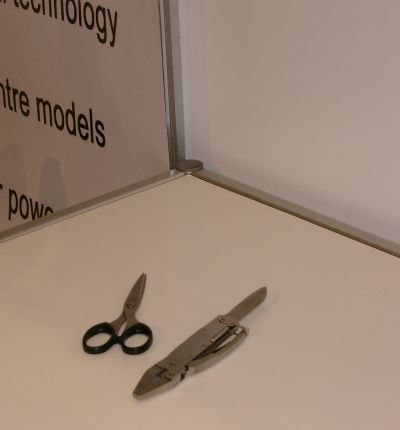
| The system includes also a X-Ray and metal screening system. Two days before we were in the Congress bringing all kind of boxes and equipment. No physical access security was implemented until the very late time and we could move inside freely carrying any items. |
| Days before the Summit no physical security was available. Anyone could bring anything inside the conference. We wonder if all the data collected about the participants is proportional and balanced. In the name of SECURITY the participants are pictured and screened, a huge database is created. What for? To protect whom? |
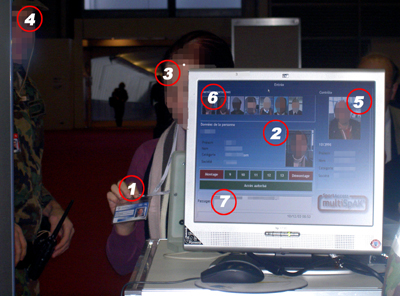
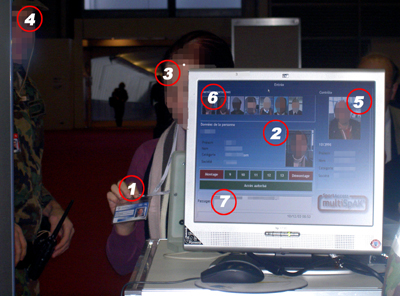
| 1. This is the first time that the participant is aware what is carrying is not just a simple plastic card.
2. Upon request to the radio smart card, the picture and the rest of the personal data is requested from the database.
3. The picture in the badge, the picture in the terminal and the cardholder face are verified.
4. Physical Verification of the pictures is done by the Swiss Army dressed in uniform.
5. Data of the participants that entered the Congress just before is also visible in the screenshot. Notice that is possible to make pictures of the personal data.
6. A set of pictures of the people latest visitors is available. The system timestamps every entry.
7. A timestamp shows the last time that the participants entered the Congress.
|